Protecting Devices and Data in the Quantum Era
Quantum computers will eventually become powerful enough to break traditional asymmetric cryptographic methods, that is, some of the most common security protocols
Home > Webinars
Check out our library of upcoming and on-demand webinars, and hear from our experts about topics ranging from high speed memory solutions, security IP, IoT and beyond.

Quantum computers will eventually become powerful enough to break traditional asymmetric cryptographic methods, that is, some of the most common security protocols

A side-channel attack (SCA) is a security exploit that attempts to extract secrets from a chip or a system. This presentation will

Automotive systems, and the semiconductors used within them, are some of the most complex electronics seen today. That complexity is set to

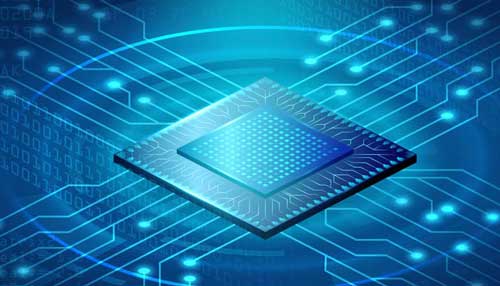
Data centers continue to adopt full line-rate security at various levels and use cases. Layer 2 (MACsec) and Layer 3 (IPsec) protocols

There is a growing industry consensus on the imperative of incorporating memory encryption in computing architectures for protecting data in use. Designing

The semiconductor industry is the lifeblood of the digital economy. The design, manufacturing and consumption of chips is a global ecosystem, and
This webinar will explore how GDDR6, operating at data rates up to 24 Gigabits per second (Gb/s) supports the memory and performance
The latest generation of PCI Express® (PCIe®) 6.0, advances performance to 64 GT/s in support of advanced data center workloads and networking.

Vehicle systems and the semiconductors used within them represent some of today’s most complex electronics. In the drive to autonomous vehicles, increasingly

Vehicle systems and the semiconductors used within them are some of the most complex electronics seen today. Ensuring these systems are both

There are many challenges to achieving good “memory security,” especially in that the term “memory” could refer to on-chip SRAM, embedded non-volatile
The semiconductor industry is the lifeblood of the digital economy. The design, manufacturing and consumption of chips is a global ecosystem, and

Certification is increasingly important across many vertical markets and, as systems become more integrated, across sectors. It is critical to trust the
Network security at full line rate became de-facto requirement across multiple markets and applications. Layer 2 (MACsec) and Layer 3 (IPsec) are

In modern communication networks, and especially moving to zero trust environments, all communication channels, including local memory interfaces must be secured. Hardware